Cryptographic hash functions serve as the unsung heroes in the digital world, providing a strong layer of security to safeguard our sensitive data. This article delves into the inner workings of these remarkable algorithms, examining their applications, strengths, and significance in ensuring the confidentiality, integrity, and authenticity of information.
Key Takeaways:
- Hash functions are mathematical functions that convert a set of data into a fixed-size bit string called a hash value.
- These functions play a crucial role in cryptography and have varying levels of complexity and difficulty.
- Cryptographic hash functions are widely used in applications such as cryptocurrencies, password security, and message security.
In the era of digitization, securing data has become an utmost concern. Whether it involves protecting personal information or safeguarding financial transactions, the need for impenetrable codes has never been greater. Cryptographic hash functions step in as the digital guardians that ensure the integrity and security of our data. But what exactly are cryptographic hash functions, and how do they work their magic?
This article embarks on a captivating journey into the realm of cryptographic hash functions. We unravel the secrets behind their unbreakable codes, explore their practical applications, and understand why they are indispensable tools for maintaining digital security. So, fasten your seatbelts as we embark on this exhilarating adventure!
I. Understanding Cryptographic Hash Functions: The Building Blocks of Security
What Are Cryptographic Hash Functions?
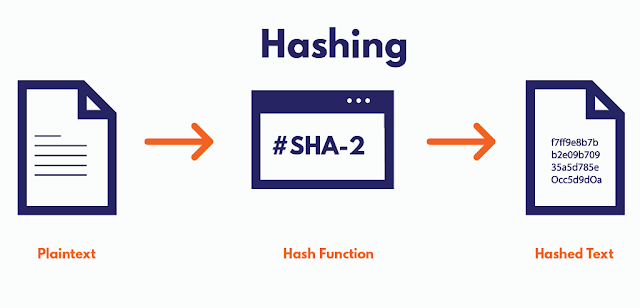
Cryptographic hash functions are mathematical algorithms that take an input (or message) and produce a fixed-size string of characters known as a hash value or digest. These algorithms are designed to be fast, efficient, and irreversible, making it practically impossible to retrieve the original input from the hash value alone. Think of it as a one-way street—easy to go from input to hash, but incredibly difficult to reverse the process.
Properties of Cryptographic Hash Functions
Effective cryptographic hash functions must possess several essential properties:
a. Deterministic: A cryptographic hash function always produces the same hash value for the same input.
b. Pre-image resistance: It is computationally infeasible to determine the original input from the hash value.
c. Collision resistance: The likelihood of two different inputs producing the same hash value is highly improbable.
d. Avalanche effect: Even a slight change in the input should result in a significantly different hash value.
II. Applications of Cryptographic Hash Functions: Beyond Digital Locks
Data Integrity Verification
Cryptographic hash functions play a crucial role in ensuring data integrity. By comparing the hash value of a file before and after transmission, one can easily detect any changes or tampering that occurred during transit. This capability makes hash functions invaluable in fields such as file sharing, software updates, and digital forensics.
Password Storage
Secure password storage is paramount to prevent unauthorized access. Hash functions, combined with additional security measures like salting and key stretching, provide a robust defense against password breaches. Instead of storing actual passwords, only their hash values are stored. When a user logs in, their password is hashed and compared to the stored hash, granting access if they match.
III. Cryptographic Hash Functions in Blockchain Technology
Building Blocks of Blockchain
Cryptographic hash functions serve as the building blocks of blockchain technology, enabling its decentralized and tamper-resistant nature. Each block in a blockchain contains a hash value that uniquely identifies it and links it to the previous block. Any alteration to a block's data will result in a different hash value, alerting the network to potential tampering.
Proof of Work
Cryptocurrencies like Bitcoin rely on cryptographic hash functions for their consensus mechanism, known as Proof of Work (PoW). Miners compete to find a hash value that meets specific criteria, requiring substantial computational effort. This process not only secures the network but also ensures the fair distribution of newly minted coins.
IV. Addressing Common Misconceptions About Cryptographic Hash Functions
Cryptographic Hash Functions Are Not Encryption
While cryptographic hash functions and encryption both involve transforming data, they serve different purposes. Hash functions are irreversible and primarily used for data integrity verification, whereas encryption algorithms are reversible and used for confidentiality.
Cryptographic Hash Functions Are Not Foolproof
Although cryptographic hash functions are highly secure, they are not immune to all attacks. With technological advancements, new vulnerabilities may emerge. Staying updated with the latest algorithms and recommended best practices is crucial to ensuring ongoing security.
V. The Future of Cryptographic Hash Functions: Innovations and Challenges
As technology evolves, cryptographic hash functions face new challenges. Quantum computing poses a potential threat to currently used algorithms, necessitating the development of quantum-resistant hash functions. Researchers worldwide are actively exploring post-quantum cryptography to mitigate this risk and ensure the longevity of digital security.
Cryptographic hash functions are designed to transform an input (message) of any size into a fixed-size output called a hash value or digest. These functions are designed to satisfy certain security properties and are widely used in various applications to ensure data integrity and security.
Here's a high-level overview of how cryptographic hash functions work:
1. Input: The hash function takes an input, which can be a message, file, or any data of arbitrary length.
2. Compression: The input is processed through a compression function that operates on fixed-size blocks of data. The compression function applies a series of mathematical operations, such as bitwise operations, modular arithmetic, and logical functions, to transform the input data.
3. Iteration: To handle inputs of any length, the compression function is applied iteratively to process each block of data. The output of one iteration becomes the input for the next iteration until all the blocks are processed.
4. Finalization: Once all the blocks have been processed, a finalization step is performed to generate the fixed-size hash value. This step may involve additional operations, such as XORing, shifting, and modular arithmetic, to produce the final hash value.
The resulting hash value is a unique representation of the input data. Even a small change in the input will produce a completely different hash value. This property, known as the avalanche effect, ensures that even minor modifications in the input will result in a significantly different output.
Cryptographic hash functions are designed to be computationally difficult to reverse, meaning it is practically infeasible to derive the original input from the hash value alone. Additionally, they should be resistant to collisions, meaning it should be highly unlikely for two different inputs to produce the same hash value.
Commonly used cryptographic hash functions include the SHA-2 family (such as SHA-256 and SHA-512) and the more recent SHA-3 family. These hash functions have undergone rigorous analysis and are widely trusted for their security properties.
It's important to note that cryptographic hash functions are just one component of a larger cryptographic system. Depending on the application, additional measures such as encryption, digital signatures, and key management may be necessary to achieve comprehensive data security.
Cryptographic hash functions transform input data into fixed-size hash values, ensuring data integrity, authentication, and other security properties. They are designed to be computationally difficult to reverse and resistant to collisions, making them valuable tools for ensuring the security of digital systems and protecting sensitive information.
Cryptographic hash functions possess several important properties:
1. Deterministic: A given message always produces the same hash value, ensuring consistency.
2. Fast Computation: The hash value is computed quickly, allowing for efficient processing.
3. Collision Resistance: It is highly improbable for two different messages to yield the same hash value, preventing unintended collisions.
4. Preimage Resistance: It is computationally infeasible to generate a message that matches a specific hash value, ensuring the integrity of the hash function.
5. Avalanche Effect: Even slight modifications to the input message result in significant changes to the resulting hash value, providing increased security and preventing correlation with the original message.
Commonly used cryptographic hash functions include MD5, SHA-1, and SHA-2. The uniqueness of each hash is crucial for the integrity of cryptographic hash functions, as it ensures that each message is identified uniquely and cannot be feasibly duplicated.
Digital signature schemes, website file downloads, and password security rely on cryptographic hashes. Digital signatures involve calculating the hash of a message to verify its integrity, while websites often publish hash values for downloadable files to allow users to independently verify the file's integrity. In password security, passwords are hashed and compared to stored hashes to authenticate users securely.
SHA-1 (Secure Hash Algorithm 1) is a cryptographic hash function that takes an input message and produces a fixed-size digest of 160 bits, typically represented as a 40-character hexadecimal number. It was designed by the National Security Agency (NSA) and published by the National Institute of Standards and Technology (NIST) in 1995.
However, SHA-1 is now considered insecure for most cryptographic purposes due to vulnerabilities that have been discovered over time. These vulnerabilities make it susceptible to collision attacks, where two different messages can produce the same hash value. As a result, SHA-1 is no longer recommended for cryptographic security.
In response to these vulnerabilities, newer and more secure hash functions have been developed, such as SHA-2 (including SHA-256, SHA-384, and SHA-512) and SHA-3. These newer algorithms provide stronger security and resistance against cryptographic attacks.
It is important to note that the usage of SHA-1 certificates is no longer compliant with industry standards, such as the CA/B Forum Baseline Requirements, and major web browsers no longer support them. The transition to more secure hash functions, such as SHA-256, is recommended for ensuring the integrity and security of digital communications.
SHA-2 (Secure Hash Algorithm 2) is a family of cryptographic hash functions that includes SHA-224, SHA-256, SHA-384, and SHA-512. These algorithms are designed to take an input message of any length and produce a fixed-size digest. The digest sizes for SHA-2 are 224, 256, 384, and 512 bits, respectively.
Among the SHA-2 functions, SHA-256 (the 256-bit variant) is the most commonly used. It produces a 256-bit digest, represented as a 64-character hexadecimal number.
SHA-2 is widely used for various cryptographic applications, such as digital signatures, data integrity verification, and password hashing. It offers significantly stronger security compared to its predecessor, SHA-1, and is considered to be secure for most practical purposes.
The different digest sizes in the SHA-2 family provide flexibility for different security requirements. For instance, SHA-224 and SHA-256 are commonly used in applications where a 128-bit security level is desired, while SHA-384 and SHA-512 provide even stronger security with larger digest sizes.
SHA-2 has been widely adopted and is supported by various cryptographic libraries and protocols. It is considered a reliable choice for cryptographic hash functions in modern security systems.
Cryptographic hash functions are designed to be one-way functions, meaning it is computationally infeasible to reverse the process and retrieve the original input (plaintext) from the hash value (checksum). The irreversible nature of cryptographic hash functions is a critical security property that ensures the integrity and confidentiality of the hashed data.
However, as you mentioned, there are techniques like rainbow tables that attempt to find the plaintext corresponding to a given hash value. Rainbow tables are precomputed tables containing pairs of plaintext and their corresponding hash values. When a hacker has access to such a table, they can quickly look up the hash value and find the corresponding plaintext.
The effectiveness of rainbow tables depends on the size and complexity of the input space (possible plaintexts). For simple and commonly used passwords, rainbow tables can be quite effective, which is why it's essential to use strong and complex passwords to increase security.
To enhance the security of cryptographic hash functions against such attacks, salting is commonly used. A salt is a random value appended to the plaintext before hashing, resulting in a unique hash value for each input, even if the plaintexts are the same. Salting prevents the use of precomputed tables, as each entry in the table would need to be computed separately for every possible salt value, which is not practical for large salt spaces.
In summary, while cryptographic hash functions are not entirely foolproof against all attacks, they still play a crucial role in securing sensitive data, and using additional techniques like salting can further enhance their effectiveness against rainbow table attacks.
More Information on Cryptographic Hash Functions
It might seem like cryptographic hash functions are related to encryption, but the two work in different ways.
Encryption is a two-way process where something is encrypted to become unreadable and then decrypted later to be used normally again. You might encrypt files you've stored so that anyone who accesses them is unable to use them, or you can use file transfer encryption to encrypt files that are moving over a network, like the ones you upload or download online.
Cryptographic hash functions work differently, in that the checksums aren't meant to be reversed with a special dehashing password. The only purpose CHFs serve is to compare two pieces of data, such as when downloading files, storing passwords, and pulling data from a database.
It's possible for a cryptographic hash function to produce the same checksum for different pieces of data. When this happens, it's called a collision, which is a huge problem considering the entire point of the function is to make unique checksums for every data input into it.
Collisions can occur is because each CHF produces a value of a fixed length regardless of the input data. For example, the MD5 cryptographic hash function generates 827ccb0eea8a706c4c34a16891f84e7b, 1f633b2909b9c1addf32302c7a497983, and e10adc3949ba59abbe56e057f20f883e for three totally different blocks of data.
The first checksum is from 12345. The second was generated from over 700 letters and numbers, and the third is from 123456. All three inputs are of different lengths, but the results are always just 32 characters long, since MD5 checksum was used.
There's no limit to the number of checksums that could be created because each tiny change in the input is supposed to produce a completely different checksum. Because there is a limit to the number of checksums that one CHF can produce, there's always the possibility that you'll encounter a collision.
This is why other cryptographic hash functions have been created. While MD5 generates a 32-character value, SHA-1 generates 40 characters and SHA-2 (512) generates 128. The greater the number of characters the checksum has, the less likely that a collision will occur.
If you find my articles enjoyable, I invite you to subscribe to my Newsletter.
By subscribing, you'll stay updated with my latest content and receive valuable information directly in your inbox.
Don't miss out on this opportunity!
Enter your email address below to SUBSCRIBE.
Rest assured, My Newsletter is free and spam-free.
Comments
Post a Comment